Recent Articles
How To Recover Overwritten Files
The Snowflake Data Breach: A Comprehensive Overview
Mac Not Recognizing External Hard Drive: Quick Fix Solutions
How Multi-Cloud Backup Solutions Can Prevent Data Disasters
Capibara Ransomware: What is it & How to Remove
What Should a Company Do After a Data Breach: The Ticketmaster Incident
Secles Ransomware: Removal Guide
What To Do When Your Chromebook Freezes
How to Create Hyper-V Backup
What Is The Best Data Recovery Software For PC

I think there's an issue with my storage device, but I'm not sure Start a free evaluation →
I need help getting my data back right now Call now (800) 972-3282
DarkRace ransomware is a type of malware that encrypts files, appends its unique extension to filenames (“.1352FF327”), and creates a ransom note demanding payment in exchange for the decryption key.
The executable is a 32-bit GUI-based Microsoft Visual C/C++ application identified by its SHA256 hash value. DarkRace is a relatively new ransomware group that has claimed responsibility for several attacks.
SalvageData experts recommend proactive data security measures, such as regular backups, strong cybersecurity practices, and keeping software up to date, to protect against ransomware attacks. And, in case of a ransomware attack, contact our ransomware recovery experts immediately.
What kind of malware is DarkRace?
DarkRace is ransomware, which is a type of malware that encrypts and locks the victims’ files and then requests a ransom in exchange for the decryption key.
It encrypts files, appends the .1352FF327 extension to filenames, and creates a ransom note demanding payment in exchange for the decryption key. DarkRace is a relatively new ransomware group that has claimed responsibility for several attacks, including the hep Global data breach in Germany.
Everything we know about DarkRace Ransomware
Confirmed Name
- DarkRace virus
Threat Type
- Ransomware
- Crypto Virus
- Files locker
- Double extortion
Encrypted Files Extension
- .1352FF327
Ransom Demanding Message
- Readme.1352FF327.txt
Is There a Free Decryptor Available?
No, DarkRace ransomware does not have a decryptor
Detection Names
- Avast Win32:RansomX-gen [Ransom]
- AVG Win32:RansomX-gen [Ransom]
- Emsisoft Trojan.GenericKD.67391585 (B)
- Kaspersky HEUR:Trojan-Ransom.Win32.Generic
- Malwarebytes Ransom.FileCryptor
- Microsoft Ransom:Win32/DarkTrace.MA!MTB
Distribution methods
- Known software vulnerabilities
- Phishing emails
- Social engineering
- Cracked software installations
Consequences
- Files are encrypted and locked until the ransom payment
- Data leak
- Double extortion
DarkRace ransomware IOCs
- Encrypted files
- A ransom note named Readme.1352FF327.txt on the infected machine
How do you find DarkRace ransomware’s ransom note
DarkRace ransom note has the TOR website where they threaten to leak the victim’s data into. The note also says that the gang is not politically motivated, but is interested only in the money.
The DarkRace ransom note also contains the victim’s personal Decryption ID.
This is a sample of the DarkRace ransom note:

It is important to note that paying the ransom does not guarantee that the files will be decrypted, and it may encourage ransomware groups to continue their criminal activities. Organizations can mitigate the risk of ransomware attacks by implementing security measures such as keeping software up to date, using strong passwords, enabling two-factor authentication, and training employees on how to identify and avoid phishing emails
Contacting SalvageData ransomware removal experts provides you with a secure data recovery service and ransomware removal after an attack.
How does DarkRace ransomware spread
- Known software vulnerabilities. Hackers use software with known vulnerabilities to attack businesses as well. That’s why it’s very important to also keep every software updated and protect remote administration tools like Remote Desktop Protocol (RDP).
- Cracked software installations. Hackers use obfuscator technology in combination with other methods to infect the device without the user being aware. Cracked software installations allow malicious files to enter the system.
- Spam email campaigns. This a phishing email attack where hackers use social engineering to deceive victims into clicking malicious links or attachments. After that, the exploit kit is downloaded into the machine and the threat actors can trigger ransomware at any moment. These emails can be targeted when hackers intend to access a specific business or can be non-targeted phishing when they send a mass malware spam campaign.

How does DarkRace ransomware infect a system
DarkRace ransomware works by following a typical ransomware attack pattern. While specific details about DarkRace ransomware are limited, we can infer how it operates based on general knowledge about ransomware attacks. Here is a breakdown of how DarkRace ransomware likely works:
1. Initial infection
DarkRace ransomware gains access to a computer or network through various methods, such as exploiting software vulnerabilities, phishing emails, brute-force attacks, or Remote Desktop Protocol (RDP) attacks.
2. File encryption
Once inside the system, DarkRace ransomware starts encrypting files on the infected machine and potentially on connected network drives. It appends its own extension (e.g., “.1352FF327”) to the filenames, making the files inaccessible without the decryption key.
3. Ransom note
DarkRace ransomware creates a ransom note that is typically displayed to the victim. It includes instructions on how to pay the ransom, a deadline for payment, and a warning not to attempt to decrypt the files without the decryption key or delete the encrypted files.
4. Ransom payment
The ransom note demands payment in exchange for the decryption key. The attackers usually require payment in cryptocurrencies like Bitcoin to make it difficult to trace the transactions.
Do not pay the ransom! Contacting a ransomware removal service can not only restore your files but also remove any potential threat.
How to handle a DarkRace ransomware attack
Important: The first step after identifying DarkRace IOCs is to resort to your Incident Response Plan (IRP). Ideally, you have an Incident Response Retainer (IRR) with a trusted team of professionals that can be contacted 24/7/365, and they can take immediate action that will prevent data loss, reduce or eliminate the ransom payment, and help you through any legal liabilities.
To the best of our knowledge with the information we have at the time this article is published, the first step that a team of ransomware recovery experts would take is to isolate the infected computer by disconnecting it from the internet and removing any connected device.
Simultaneously this team will assist you in contacting your country’s local authorities. In the case of US residents and businesses, it is the local FBI field office and the Internet Crime Complaint Centre (IC3).
To report a ransomware attack you must gather every information you can about it, including:
- Screenshots of the ransom note
- Communications with threat actors (if you have them)
- A sample of an encrypted file
However, if you don’t have an IRP or IRR, you can still contact ransomware removal and recovery professionals. This is the best course of action and greatly increases the chances of successfully removing the ransomware, restoring the data, and preventing future attacks. We recommend that you leave every infected machine as they are and call an emergency ransomware recovery service.
Restarting or shutting down the system may compromise the recovery process. Capturing the RAM of a live system may help get the encryption key, and catching a dropper file might be reverse-engineered and lead to the decryption of the data or understanding of how it operates.
1. Contact your Incident Response provider
A Cyber Incident Response is the process of responding to and managing a cybersecurity incident. An Incident Response Retainer is a service agreement with a cybersecurity provider that allows organizations to get external help with cybersecurity incidents. It provides organizations with a structured form of expertise and support through a security partner, enabling them to respond quickly and effectively during a cyber incident.
An incident response retainer offers peace of mind to organizations, offering expert support before and in the aftermath of a cybersecurity incident. An incident response retainer’s specific nature and structure will vary according to the provider and the organization’s requirements. A good incident response retainer should be robust but flexible, providing proven services to enhance an organization’s long-term security posture.
If you contact your IR service provider, they will care for everything else. However, if you decide to remove the ransomware and recover the files with your IT team, then you can follow the next steps.
2. Identify the ransomware infection
You can identify which ransomware infected your machine by the file extension (some ransomware uses the file extension as their name), using a ransomware ID tool, or it will be on the ransom note. With this information, you can look for a public decryption key.
You can also check the ransomware type by its IOCs. Indicators of Compromise (IOCs) are digital clues that cybersecurity professionals use to identify system compromises and malicious activities within a network or IT environment. They are essentially digital versions of evidence left at a crime scene, and potential IOCs include unusual network traffic, privileged user logins from foreign countries, strange DNS requests, system file changes, and more. When an IOC is detected, security teams evaluate possible threats or validate its authenticity. IOCs also provide evidence of what an attacker had access to if they did infiltrate the network.
3. Remove the ransomware and eliminate exploit kits
Before recovering your data, you must guarantee that your device is ransomware-free and that the attackers can’t make a new attack through exploit kits or other vulnerabilities. A ransomware removal service can delete the ransomware, create a forensics document for investigation, eliminate vulnerabilities, and recover your data.
4. Use a backup to restore the data
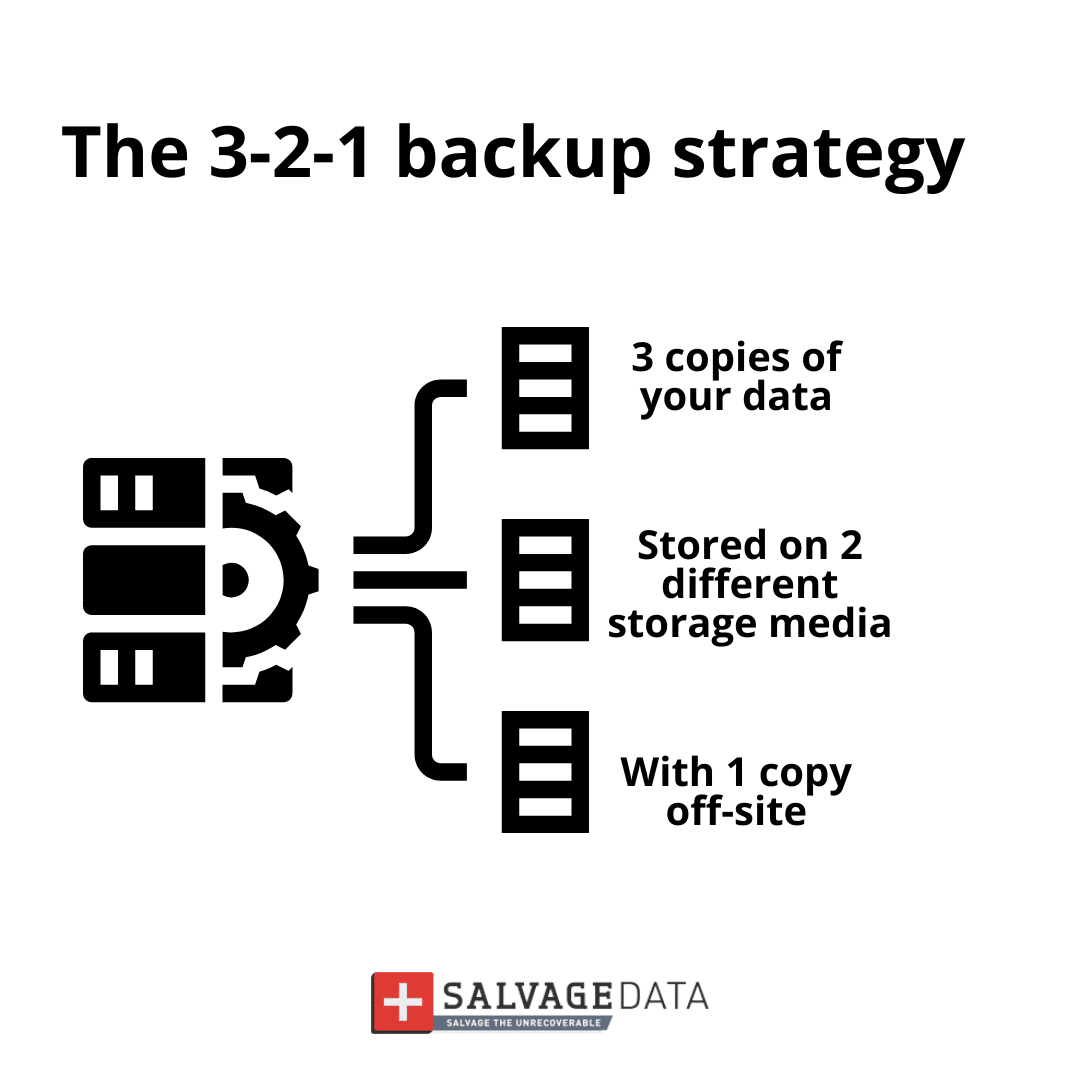
Backups are the most efficient way to recover data. Make sure to keep daily or weekly backups, depending on your data usage. Also, apply the 3-2-1 backup rule.
5. Contact a ransomware recovery service
If you don’t have a backup or need help removing the ransomware and eliminating vulnerabilities, contact a data recovery service. Paying the ransom does not guarantee your data will be returned to you. The only guaranteed way you can restore every file is if you have a backup of it. If you don’t, ransomware data recovery services can help you decrypt and recover the files.
SalvageData experts can safely restore your files and prevent DarkRace ransomware from attacking your network again.
Contact our experts 24/7 for emergency recovery service.
Prevent the DarkRace ransomware attack
Preventing ransomware is the best solution for data security. is easier and cheaper than recovering from them. DarkRace ransomware can cost your business’s future and even close its doors.
These are a few tips to ensure you can avoid ransomware attacks:
- Install antivirus and anti-malware software.
- Utilize strong and secure passwords.
- Keep software and operating systems up to date.
- Implement firewalls.
- Create a data recovery plan.
- Regularly schedule backups.