Since its creation in the 2010s, cloud storage technology has grown quickly as a game-changer in data storage. Storing documents and photos in the cloud now represents a helpful option. It offers many ranges of benefits, such as affordable prices, flexibility, automatic software updates, remote management, and automatic backup.
Organizations and users worldwide prefer to manage their data on cloud-based platforms these days rather than create an on-site data center. Over 70% of global businesses operate in the cloud. Meanwhile, private users entrust cloud environments with terabytes of personal data, such as photo albums, documents, sensitive files, and so on. Cloud visibility and control tools, along with unceasing improvement of machine learning implements, predictive analysis, and artificial intelligence, allow providing extra levels of security, hence lowering the chances of breaches and security failures in prospect. Technology itself is not 100% foolproof: information on the cloud platform is vulnerable to the same threats as the internet.
For those trusting their backup only to the cloud, be aware: cloud service may lose your data. For this, you must know how to protect your cloud data.
Top Summary: No cloud service can guarantee complete and flawless security of your data. Still, you can protect your cloud account and prevent cloud data loss.
What are cloud data threats?
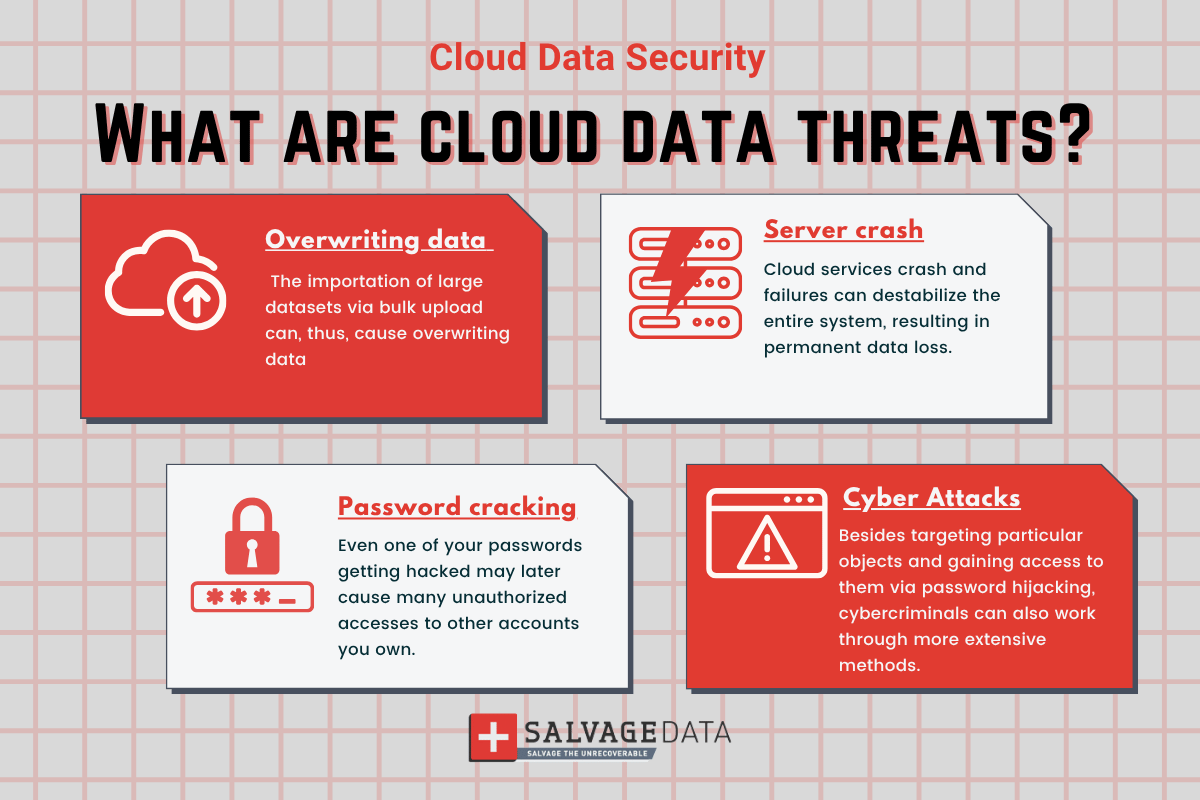
While it’s unlikely that a major online service vendor will lose your data permanently, or encounter a complete service outage, several causes of data loss can occur because:
Overwriting data
On cloud-based applications, it is possible to add and update large amounts of information. The importation of large datasets via bulk upload can, thus, cause overwriting data. Another cause is when a third-party application is used to manage the upload.
Password cracking
Online services keep large amounts of both private users’ sensitive information and companies’ crucial corporate data. One reason why it greatly interests hackers. It is important to understand that even one of your passwords getting hacked may later cause many unauthorized accesses to other accounts you own. The risk grows if you use the same cloud storage service or the same password for the different accounts.
Cyber attacks
No matter how enormous volumes of information are in the cloud, you are still at risk of a data breach. Besides targeting particular objects and gaining access to them via password hijacking, cybercriminals can also work through more extensive methods. For instance, an attack like distributed-denial-of-service (DDOS-attacks) can disrupt the composition of stored information, leading to massive breaches.
A server crash or outage
Cloud services crash and failures can destabilize the entire system, resulting in permanent data loss. Although this kind of disaster is rare, the fact of the possibility should convince you to consider taking extra measures to ensure the best protection of your data.
Summary: From cyberattacks to server outages, you must prepare yourself for any issue to preserve your data. Learning what can go wrong helps with data loss prevention.
Security measures to prevent cloud data loss
One important tip we can give is to make a backup of the most important files, like photos and sensitive data, to a storage device (an external HD is a good option). This can reassure you that you can have your data no matter what.
As for the data you keep in the cloud, there are a few actions you can take to guarantee its safety.
Create unique passwords for accounts
Make sure you don't use the same password elsewhere. When you create a unique password for each of your accounts, you avoid a hacker accessing them all in case of an attack. A password manager can help enhance safety by generating hard-to-guess passwords and saving them on devices you use to access your accounts. Remember to provide proper protection for your devices since, in case of physical theft, all the saved passwords are at risk.
Apply two-factor authentication
You’ll receive a notification if anyone but you try to access your account once you activate two-factor authentication. This method, though, is not flawless, but it grants you the possibility to secure the information stored in your accounts from threats like cyber-attacks. Also, when the option is there, you can select questions only you know the answer to in a password setup process.
Review connected accounts
If your work implies sharing access to your cloud data storage, reviewing connected accounts is another important step in securing its contents. Remove any connected accounts you discontinued, as they might become a gateway for hackers to access your current account. Always remember to keep lists clean on both cloud storage services and social media networks to prevent it.
Multiple backups
Setting up the automated backup (cloud-to-cloud backup) would also be a wise thing to do. Regardless of what guarantees the cloud provider makes, you should always backup your most crucial information to a few services at a time. The SLA (Service Level Agreement) that you receive will only cover you for the cost of the service, not for the value of the stored information, so it’s in your best interest to preserve that information in multiple places. Creating a few copies on an external hard drive is an option, too.
Encryption means safety
For sensitive information, it’s vital to encrypt the data on your server before placing it in the cloud. You can use a cloud service that offers local decryption besides storage instead of performing it on your own. It also reduces the possibility that service providers or server administrators will be able to access your data (also referred to as zero-knowledge privacy).
Summary: The more you do to prevent data loss, the higher your chances of always having it. Even though cloud services are very secure, they are not flawless. Encrypt sensitive data, use strong and different passwords for each account, and even make more than one backup will guarantee your data last.
These are the most secure ways of minimizing the chances of losing the information you keep in cloud-based storage. And finally, apart from following the tips mentioned above, remember to get to know service providers as much as you can.
And, for any questions about cloud data recovery, you can always contact one of SalvageData’s experts.